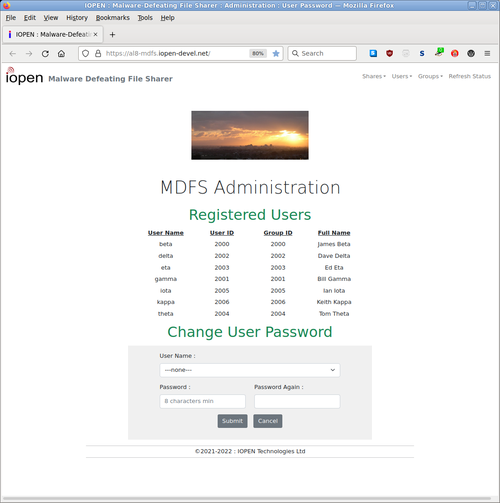
Version 1.2 website shown. Currently at v2.1 - More options and dark theme.
"Just because the tiger hasn't bitten you doesn't mean it won't. And when it does it'll hurt."
On conventional business IT systems, by the time you detect signs of a breach it's almost certainly too late to prevent major operational flow disruption and big costs.
Preventing and limiting business OpFlow disruption is what really matters. If only because the cost of prevention is far less than the cost of recovery.
Do facts and reality matter to you? If so, then read on ...
A US IT security company has found that only around 10% of business IT breaches get publicly reported, so the risk is much greater than generally assumed and the safety margins much smaller. It's also still the case that "one wrong click and you're gone".
So there's an urgent need to identify and eliminate the IT safety gaps.
But what incentives do those who sell you 'security' subscriptions have to eliminate the gaps? Here's one opinion.
Fortunately for businesses, we've done just that. Our full solution involves MDFS and DF plus a range of techniques and adjustments.
Do you want your business to remain operational in spite of malware outbreaks?
If so, please get an overview of what's involved from what follows, and then make a start on getting a quote by sending us a summary of your IT system - including the number of desktops and number of servers.
- Enabling you to concentrate on moving your business forward by greatly improving its IT resilience.
- Enabling you to maintain your business's operational flow in spite of malware by also adopting our Desktop Fallback scheme.
- Being much more effective than insurance.
- Being safer and more reliable and more economical than using 'The Cloud'.
- Having unlimited users and not having Client Access Licences.
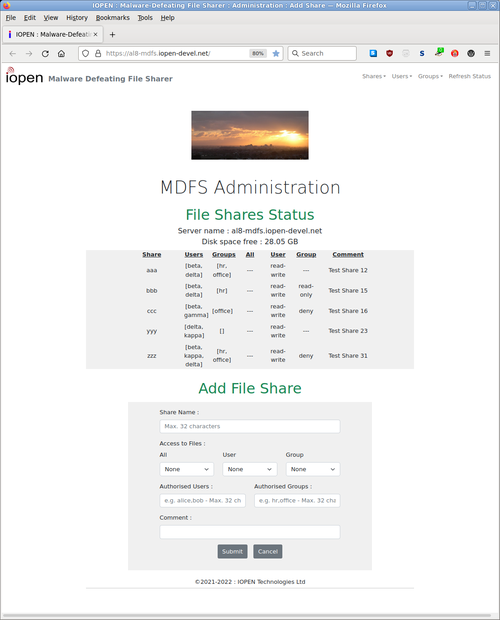
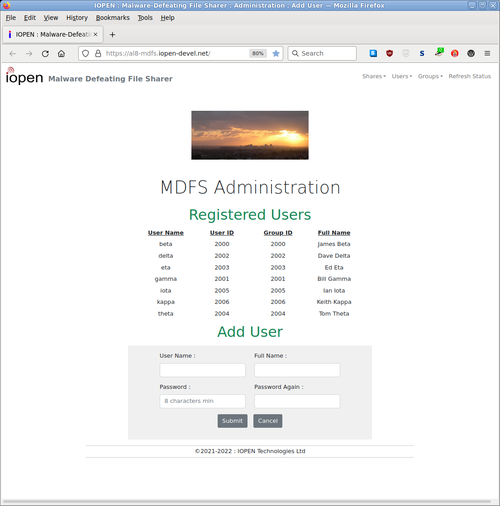
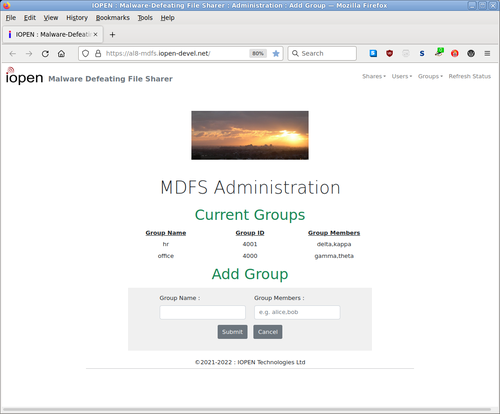
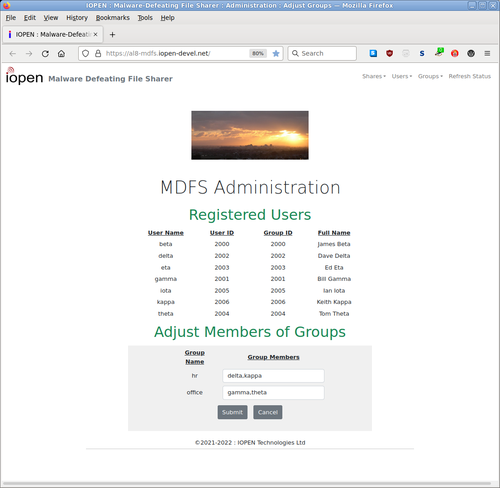
- Providing simple administration of users and shares using a web browser.
- Having long-term viability via being based on mainstream technology.
- See also our Client Experience and Graduated Benefits documents.
- Actually, there is no 'Cloud'. There's just computers owned and controlled by others. [ 1, 2 ]
- Being an MS-Windows compatible File Sharer that is naturally immune to Windows malware. Because it doesn't use Windows itself.
- Enabling you to maintain your business's operational flow in spite of malware by also adopting our Desktop Fallback scheme.
- Not relying on anti-virus software or so-called 'AI'.
- Having straightforward Windows Domain integration, where needed. But we recommend avoiding doing so if at all possible so that MDFS remains fully usable when your Domain Controllers get taken down..
- Having secure backup options : Overview and Options.
- Having its own robustness greatly enhanced by the very powerful SELinux security mechanism which, amongst its many capabilities, can defeat unknown exploits.
- Having automated monitoring, reporting, and alerting.
- Having a dedicated remote support channel (VPN) that uses quadruply-secured (4FA) access.
- Being provided as a Virtual Machine that runs an Enterprise Linux.
- All local DHCP and DNS servers should be run by non-Windows machines, for the same reason as not joining a domain.
- Remote support is required to be done from non-Windows machines.
- See also our Graduated Benefits and MDFS Structure documents.
- Improve resilience further by having Warm Spare VMs.
For any critical system correctness and production-consistency are vital.
So we've put a lot of effort into developing and verifying software that automates the production of customised VMs for clients. Based on a small plain-text specification file for each VM. MDFS is just one of the function-types of VM that the software can produce.
The production software is run on dedicated isolated VMs. Customisations include generating unique passwords and security keys for each client VM.
We can provide a free MDFS Test Drive for potential business clients. English-speaking ones initially.
Each Test Drive starts with a fresh MDFS VM running on our server. You'll need to install a Wireguard VPN client on your workstation and configure it to connect to the VM. We provide configuration details.
To make efficient use of resources we respond to what we consider to be credible requests from businesses. So if a Test Drive interests your business please make a request containing some details of your IT situation.
Implementing our full solution will save some adoptees millions of dollars, and in some cases save the business itself. Because copious evidence [ 1, 2, 3, 4 ] supports the assertion that for business users of MS-Windows the question is when, not if, a major malware-related operational disruption will occur.
You're sceptical that MDFS (in particular) can do what nobody else seems able to do reliably.
Well, MDFS is non-Windows so we don't have to contend with the 'Windows high background-noise level'. Giving us an excellent Signal-to-Noise Ratio (SNR) when looking for signs of workstation malware 'playing with' the shared files.
Its own robustness is greatly enhanced both by being naturally immune to Windows malware and by using SELinux in Enforcing mode. Note that MS-Windows still doesn't have any mechanism that's even close to SELinux's capabilities.
Background information and FAQs are here.
Terms and Conditions are here.
To avoid giving potential attackers more clues here, you'll need to request further details.
©2021-2025 : IOPEN Technologies Ltd - NZ